Kali Linux VirtualBox Update Command For Windows
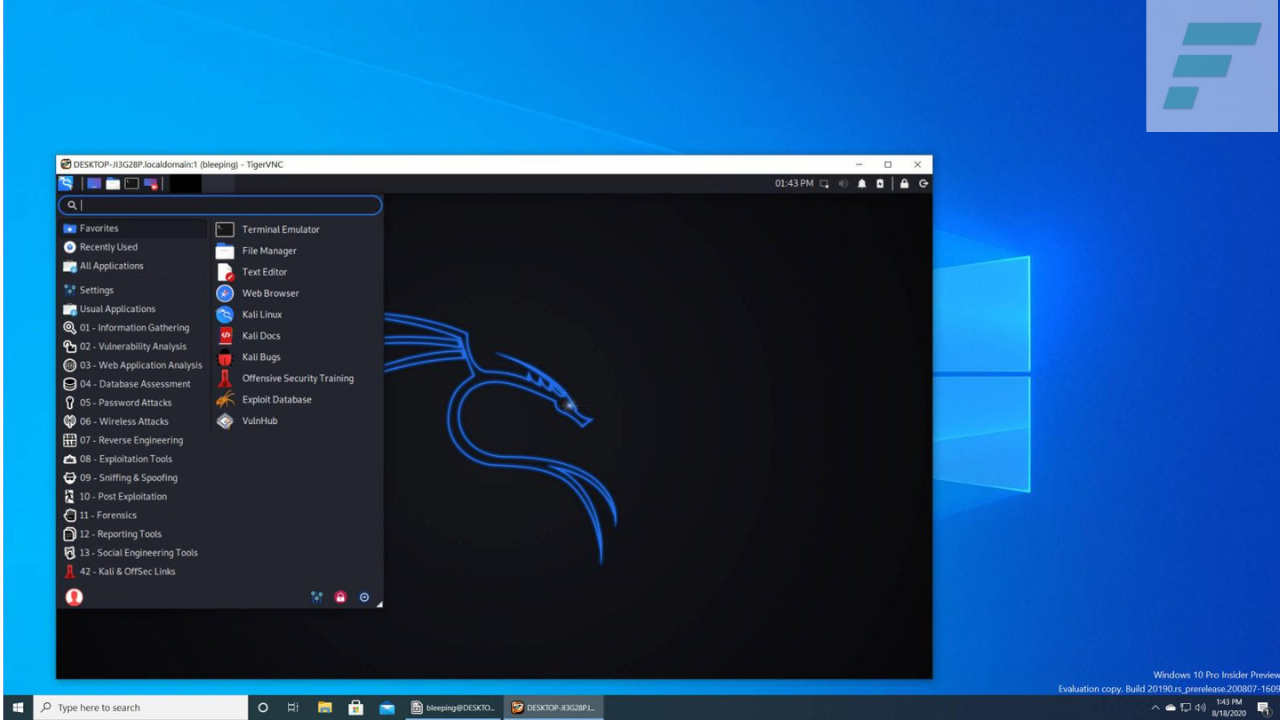
Kali Linux VirtualBox, formerly known as BackTrack Linux, is a Debian-based Linux distribution designed specifically for penetration testing, ethical hacking, and digital forensics. It is maintained and funded by Offensive Security, a renowned cybersecurity training company. Kali Linux has earned its reputation as the go-to operating system for professionals and hobbyists who seek to assess, analyze, and secure computer systems and networks.
- Penetration Testing: Kali Linux is primarily used for penetration testing, a process that involves simulating cyberattacks to identify vulnerabilities in computer systems and networks. Security professionals use Kali Linux to assess the strength of an organization’s security measures and develop strategies to strengthen them.
- Ethical Hacking: Ethical hackers employ Kali Linux to discover vulnerabilities and weaknesses in computer systems with the explicit permission of the system owner. By identifying and mitigating security flaws, ethical hackers help organizations enhance their overall cybersecurity posture.
Kali Linux VirtualBox Commands Download
Direct Download Link 1
Download Link 2
Key Features
Kali Linux boasts a vast array of features and tools that make it indispensable in the field of cybersecurity. Here are nine key features that set Kali Linux apart:
- Wide Toolset: Kali Linux includes over 600 pre-installed tools for various cybersecurity tasks, including network scanning, vulnerability assessment, password cracking, and digital forensics.
- Customization: Users can easily customize and extend Kali Linux by adding or removing tools and packages to suit their specific needs.
- Live Boot Capabilities: Kali Linux can be run directly from a bootable USB drive or DVD without the need for installation, making it an excellent choice for on-the-go security assessments.
- Full Hardware Support: It offers comprehensive hardware compatibility, ensuring that it can run on a wide range of devices and configurations.
- Regular Updates: Kali Linux receives frequent updates to keep its tools and packages up-to-date, ensuring that security professionals have access to the latest techniques and exploits.
- Forensics and Incident Response: Kali Linux includes tools and utilities for digital forensics and incident response, making it a valuable resource for investigating cybercrimes.
- Documentation: The Kali Linux community provides extensive documentation, tutorials, and resources to assist users in mastering the platform.
- Community Support: Kali Linux has a robust online community where users can seek help, share knowledge, and collaborate on cybersecurity projects.
- Security-focused: Kali Linux is designed with security in mind, incorporating features like kernel hardening and secure coding practices to minimize vulnerabilities.
What’s New?
Kali Linux continues to evolve with each new version, introducing enhanced features and tools to cater to the ever-changing landscape of cybersecurity. Here are five notable additions from recent releases:
- Kali Undercover Mode: This feature disguises the Kali Linux desktop environment to resemble Windows, making it less conspicuous during security assessments in public places.
- Kali NetHunter: An Android penetration testing platform, Kali NetHunter allows users to run Kali Linux on Android devices, turning smartphones into powerful hacking tools.
- Bleeding-Edge Repositories: Kali Linux now offers “bleeding-edge” repositories for users who want access to the latest software updates and features.
- Kali-Tools Meta-Package: A new meta-package simplifies tool management by allowing users to install a specific set of tools for different tasks, such as wireless, web, and password testing.
- Kali ARM Images: Kali Linux now supports more ARM devices, expanding its compatibility with various hardware platforms.
System Requirements
Before diving into the world of Kali Linux, it’s essential to ensure that your hardware meets the minimum requirements. Here’s a breakdown of the system requirements:
- Processor: 1 GHz x86 processor or better.
- RAM: 2 GB RAM.
- Storage: 20 GB of available disk space.
- Graphics: A graphics card capable of running a desktop environment with a resolution of 1024×768 pixels.
- Network: A wired or wireless network card that is capable of promiscuous mode for wireless reconnaissance.
How to Install
Installing Kali Linux is a straightforward process. Here’s a brief step-by-step guide:
- Download the ISO: Visit the official Kali Linux website (https://www.kali.org/downloads/) and download the appropriate ISO image for your system architecture (32-bit or 64-bit).
- Create a Bootable USB Drive: Use a tool like Rufus (on Windows) or Etcher (on Linux and macOS) to create a bootable USB drive with the Kali Linux ISO.
- Boot from USB: Insert the bootable USB drive into your computer and boot from it. You may need to change the boot order in your BIOS/UEFI settings.
- Install Kali Linux: Follow the on-screen instructions to install Kali Linux on your system. You can choose to install it alongside your existing operating system or use the entire disk.
- Configure User Account: During the installation process, you will be prompted to create a user account and set a password.
- Update and Upgrade: After installation, open a terminal and run the following commands to update and upgrade your system:
sql
sudo apt update
sudo apt upgrade
- Start Exploring: Kali Linux is now installed and ready to use. Explore its tools and resources to enhance your cybersecurity skills.
Conclusion
In conclusion, Kali Linux VirtualBox is a formidable operating system that plays a pivotal role in the world of cybersecurity. Its extensive toolkit, regular updates, and strong community support make it an indispensable asset for security professionals, ethical hackers, and enthusiasts. With its continuous evolution and commitment to security, Kali Linux remains a force to be reckoned with in the realm of ethical hacking and penetration testing. Whether you are a seasoned professional or a newcomer to the field, Kali Linux provides the tools and resources necessary to bolster your cybersecurity knowledge and skills. Embrace the power of Kali Linux and embark on a journey to safeguard digital landscapes in an increasingly interconnected world.